Top VPN Services 2026: Which Delivers Superior Performance?
In our modern digital landscape, where cybersecurity threats are omnipresent and online…
OSINT Techniques Online Privacy Investigation
It looks like we've turned accustomed to considering digital obscurity as an…
AirTag Stalking Detection Protection Methods
A woman describes an AirTag has maintained observation for extended duration. She…
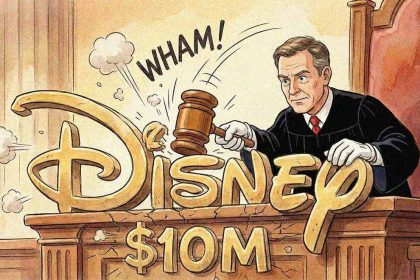
DISNEY FTC CHILDREN’S PRIVACY SETTLEMENT
Federal Court Authorizes $10 Million Settlement Between Disney and FTC for Unlawful…
GDPR Simplification Consumer Privacy Concerns
Consumer Protection Organization Raises Alarm Over European Commission's Proposed GDPR Modifications A…
BRITISH SCHOOL CYBERATTACK CLOSURE
Secondary Institution Suspends Operations Following Digital Attack, Takes All Computer Systems Offline…
ASML DATA BREACH HOAX BY THREAT ACTOR
The identical pseudo-criminal who lately claimed accountability for a fabricated NordVPN breach…
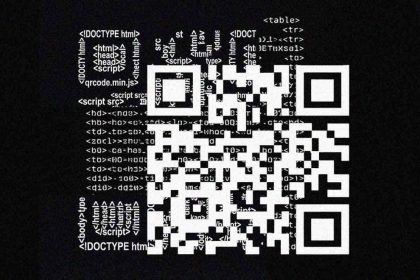
Criminals Use HTML Tables to Generate Deceptive QR Codes That Evade Email Security Systems
Malicious actors have identified a technique to circumvent detection instruments protecting email…
“Maduro capture” gains fresh significance as his Nike fleece goes out of stock
The US military's detention of Venezuela's President Nicolas Maduro has triggered social…
Chinese APT Group Exploits Cisco Email Security Flaw
A critical Cisco vulnerability currently without patches is being actively exploited by…